We are pleased to announce the 9.0 release of Topicus KeyHub. This release brings several new features and enhancements and addresses many issues found in previous versions. It is recommended to update your KeyHub deployment.
Personal vault
TKH-260 Every account in KeyHub now has access to a personal vault. This vault can be used to store personal work related passwords and keys. It is not recommended to use this vault to store private accounts because you will lose access to these passwords when your KeyHub account is revoked.
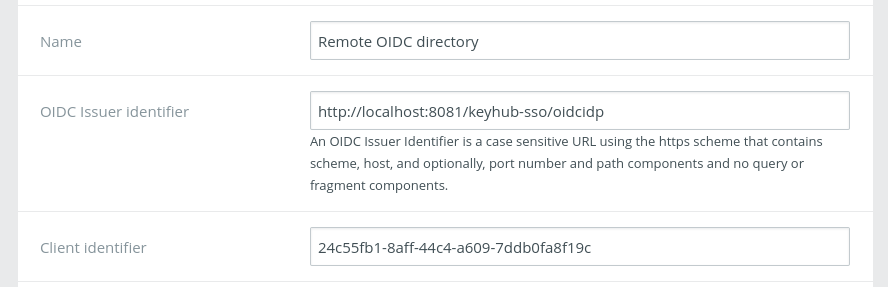
Federated identities
TKH-503 KeyHub 9.0 allows any OpenID Connect provider with discovery support to be used as a directory. This allows you to use cloud platforms such as Microsoft Azure AD and Google for authentication. You can even add one KeyHub deployment as a directory of another KeyHub deployment. Future releases will bring support for other protocols such as SAML 2.0.
Small improvements
The following smaller improvements and bugfixes were made:
TKH-499Removing KeyHub Administrators now requires approval from another administrator.TKH-587The user is now always prompted for password and 2FA at sign-on for a new session.TKH-588KeyHub now uses the officialinitiate_login_urifor IDP initiated login at the Console.TKH-590Registration wizard no longer prompts for group memberships when this is disabled for the user.TKH-591New internal accounts are now marked valid directly after activation.TKH-592The UPN for provisioned ADs no longer contains OU parts from the BaseDN.TKH-593Users are no longer prompted for their password twice when adding a new vault record.TKH-601The audit log now shows the manager who removed someone from a group.TKH-603Users can now choose their own username if enabled for a directory.TKH-604prompt=loginnow also prompts for 2FA.TKH-610Extended access can no longer be requested for dates outside the allowed range.TKH-611An error was fixed with searching for audit records with a space in the query.TKH-612An error was fixed with opening your given consent under your profile.TKH-613An error was fixed with removing multiple records from a vault.TKH-617The password foradminwas not accepted in maintenance mode.TKH-619Added missing audit records when using SSO.TKH-598TKH-599TKH-605TKH-606TKH-607TKH-608TKH-609TKH-614TKH-615Code coverage from tests was increased substantially.TKH-596TKH-600TKH-602Various styling and translation fixes.

