With some fanfare we announce the release of Topicus KeyHub 18.2, our summer holiday release. With this release we realize a long-held wish to offer our users an easier way to recover their password, including vault access. Via a social recovery protocol other users can approve the reset and recover the vault access. This same protocol will also be used to recover 2FA in case of a broken phone. As usual, we also implemented a number of smaller improvements and fixes for several issues.
Important notice: Undisclosed security vulnerability
TKH-1827 A weakness in the federated login flow used with OIDC directories was resolved. We strongly recommend all installations to be upgraded to 18.2. Topicus KeyHub users can inquire for more information.
Social recovery for password and 2FA
TKH-327 TKH-1517 TKH-1766 TKH-1787 TKH-1788 TKH-1789 We added an ability to use a social recovery protocol to safely and easily recover your access to KeyHub, including your vault access. We use a form of Shamir's Secret Sharing to safely distribute a personal recovery key among a selected set of colleagues. If at least two of these colleagues approve your password recovery, you can use the new password to login and/or access your vaults. The same protocol is use for a 2FA reset, to allow you to link new 2FA devices in case your current devices are unrecoverable.
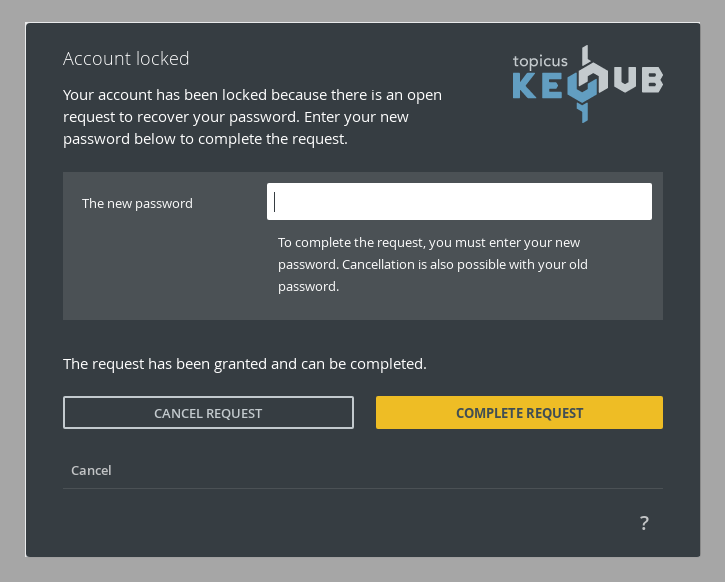
The group of colleagues is chosen from among the group managers of the groups you use the most. This determination will be re-evaluated on a regular interval. If a helpdesk group has been configured for your account, all colleagues approving account recovery will be chosen from that group.
Small improvements
The following smaller improvements and bug fixes were made:
TKH-1661We added a button in the appliance manager to force renewal of Let's Encrypt certificates, in case the automatic renewal process does not get triggered.TKH-1747Uploading a PKCS#12 (.p12/.pfx) certificate should no longer result in form validation errors if you upload the certificate before entering the password.TKH-1757Dropdown fields should once again automatically gain focus after opening.TKH-1762Manually deactivating an account now immediately invalidates all sessions for that account.TKH-1765Salt calls between our appliance manager and the VM should now in all cases refresh the authentication token if expired, leading to less errors in the log.TKH-1768We fixed a bug in our authentication process that could cause the browser extension to open new tabs in the background with every click without closing them.TKH-1769We fixed various errors on pages related to private groups.TKH-1771The /account/me and /client/me REST resources should now return the proper error status when called with the wrong credential type.TKH-1774A logout now actively closes the vault by removing the active vault session, instead of just making it inaccessible and letting it expire.TKH-1779Approving an activation request for an authorized group will once again show the requester as the one who activated the group, instead of the approver.TKH-1782It will no longer seem to be possible to transfer certain internal applications away from the 'KeyHub Administrators" group.TKH-1783The 'KeyHub Appliance Manager' application can be transferred to another group, but that group can then no longer be removed.TKH-1784We solved an error during group removal related to linked systems that could lead to a KeyHub error page and block you from removing said group.TKH-1802Shared vault records could lead to incorrect audit records or errors in cases where the source or target vault was not visible to the user.TKH-1813A starvation issue was fixed that could cause the update process to miss an available Topicus KeyHub update.TKH-1822A concurrency issue was fixed that could result in an error when changing the password. This issue was patched in version 18.2-3.

