We are proud to announce the 16.2 release of Topicus KeyHub. This release is all about internal improvements of the application and the virtual appliance. Several security issues have been fixed. We therefore strongly recommend our users to upgrade to 16.2. As usual, a number of smaller improvements have been made and several issues have been fixed. Before upgrading, please read the important notices below, especially if you are running a self-hosted docker deployment.
Important notice: Upgrading a recent installation
Topicus KeyHub appliances installed after the 8th of June 2020 (or when yum clean was run after this date) might face issues updating to the latest version. If the appliance does not detect the update to 16.2 or it fails to update, you have to run the following command on the command line (login with the keyhub user and your maintenance password):
sudo yum-config-manager --disable salt-2018.3This issue is caused by the SaltStack repository being moved to a new URL. This repository was marked vital in the appliance, causing yum to bail out. The Topicus KeyHub 16.2 update moves to a new version of SaltStack and updates the repository definitions to prevent similar issues in the future.
Important notice: Upgrading a self-hosted docker deployment
For users of our virtual appliance the steps below will be automated, however if you run Topicus KeyHub as a self-hosted docker deployment, the update to 16.2 requires two additional steps.
The first step is to specify two additional secrets as properties in the env-file. These secrets are best generated using a strong secret generator, such as the password generator in the Topicus KeyHub vault. The exact value does not matter, but it must be URL safe (such as the passwords generated by the vault). The secrets are:
ADMIN_SECRET={secret here}
CONSOLE_SECRET={secret here}In preparation to our HA setup, PostgreSQL was upgraded to 12 to make use of some of the new replication features. This means your database also has to be upgraded. The easiest way to do this is:
- Export the database
- Drop the volume and container
- Recreate the volume and start the new container
- Import the database
If you do not migrate your database or specify the new properties, Topicus KeyHub will fail to start and will become unavailable.
Important notice: Several security improvements
Topicus KeyHub 16.2 fixes several security issues identified during an independent security audit. We would like to thank Sqills and in particular Jordy Versmissen for identifying and reporting some of these issues.
TKH-1009The OAuth2 secrets for the Topicus KeyHub console and management interface were hardcoded in the binaries. Using these secrets, an attacker could get access to parts of the API that would otherwise have been shielded. Both secrets are now generated during the installation and unique per deployment.TKH-1435The Topicus KeyHub IdP has had support for PKCE for quite some time now, but both the console and management interface did not make use of it. In combination with the exposed secrets, an attacker could try to intercept an authorization code to obtain access to the API on behalf of the targeted user. PKCE is now used to protect the authorization code against these kinds of attacks.TKH-1437The rate limiting on client secrets could be abused to cause a Denial of Service for 10 minutes with just a few requests. The rate limiting is now bound to the account trying the invalid secrets, causing a lockout for just one user.TKH-1442The REST endpoint to fetch certificates for easy configuration could be abused to trigger an SSRF attack. Access to this endpoint has been restricted to the Topicus KeyHub applications only, making it very impractical to abuse.
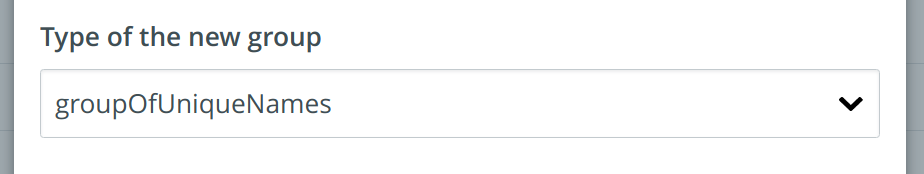
Support for other LDAP group types
TKH-1242 Topicus KeyHub used to create groups on a linked LDAP server as posixGroup only. It is now possible to select groupOfNames or groupOfUniqueNames as well. These types define the structural type of the LDAP element and have different behavior when it comes to the way members are added. Some third party applications only support on of the types. When the same KeyHub group needs to be provisioned with multiple types on the LDAP server, just create multiple groups on the LDAP server and link them to the single group in KeyHub.
Copy, move and share vault records via the CLI
TKH-1417 The Topicus KeyHub CLI received three new commands: cp, mv and share to copy, move and share vault records respectively.
Small improvements
The following smaller improvements and bug fixes were made:
TKH-981Test coverage for installing updates was improved.TKH-1164SaltStack was upgraded to version 3000.TKH-1376The IDP certificate is now displayed when editing a SAML2 application, where you often need it.TKH-1418The option to force a rotating password has been moved from a group on a linked system to the group itself.TKH-1420The location of the offline PIP repository was fixed.TKH-1421An audit log record is now recorded when a group is (un)assigned the help desk function.TKH-1424An error was fixed when trying to export the audit log with many types enabled.TKH-1425It is now possible to change the 'offline' setting when restoring a backup.TKH-1428The username was missing when requesting to make a user manager of a group.TKH-1429An error was fixed when requesting extended access for a group that is placed in a folder on the dashboard.TKH-1430The API log file was not rotated properly.TKH-1432A call to list vault records on the REST API on an empty vault would incorrectly report a 403.TKH-1433The option to update an online install using the offline update bundle is now hidden.TKH-1436TKH-1439The database was upgraded to PostgreSQL 12.TKH-1438The application server was upgraded to WildFly 20.TKH-1440Reliability of the appliance tests was improved.TKH-1441E-mail addresses now get the same prefix as provisioned accounts do to prevent conflicts.TKH-1444Unavailable yum repositories are now skipped rather than blocking the entire update.

