After two and a half years of development Topicus KeyHub has reached version 10! This new release packs many new features unique in the field of IAM. Topicus KeyHub 10 focuses on integration with other systems and tooling and addresses several issues found in previous releases. It is recommended to update your Topicus KeyHub deployment.
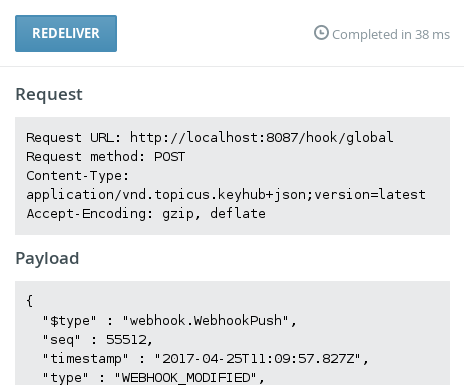
Webhooks
TKH-510 TKH-633 Webhook support probably is the most exciting new feature in this release. Any event that is recorded in the audit log can now be pushed to other systems as well. Possibilities are endless. Think of replicating your audit log on a remote system, showing alerts on monitoring systems or even reconfiguring your VPN on demand when activating groups. As part of this feature, all objects in Topicus KeyHub now have a UUID to identify them globally.
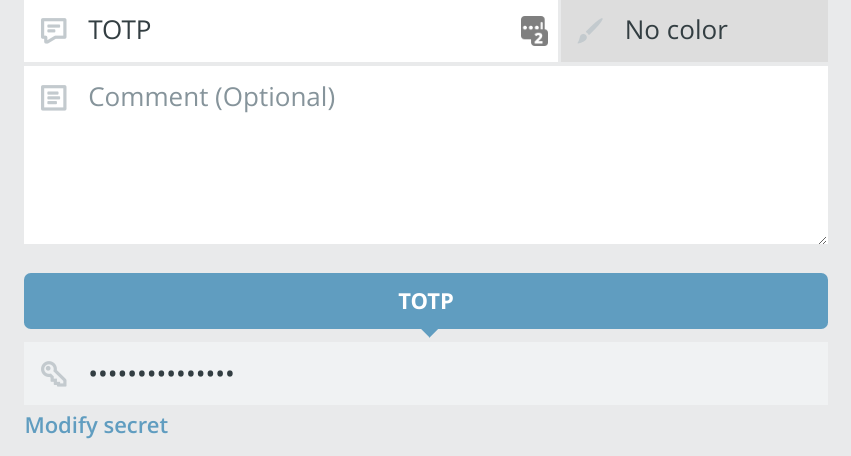
Store 2FA credentials in your vault
TKH-526 It is now possible to store TOTP secrets in the vault and share 2FA securely. Topicus KeyHub automatically calculates the 6 digit authentication code, valid only for 30 seconds, when accessing the record. As the secret is safely stored in Topicus KeyHub and cannot be retrieved, this is a very effective way of adding additional protection to your logins. When a user is removed from a group, he or she will be unable to login even when he or she stored the username and password. You cannot store the TOTP code, because it is only valid for 30 seconds.
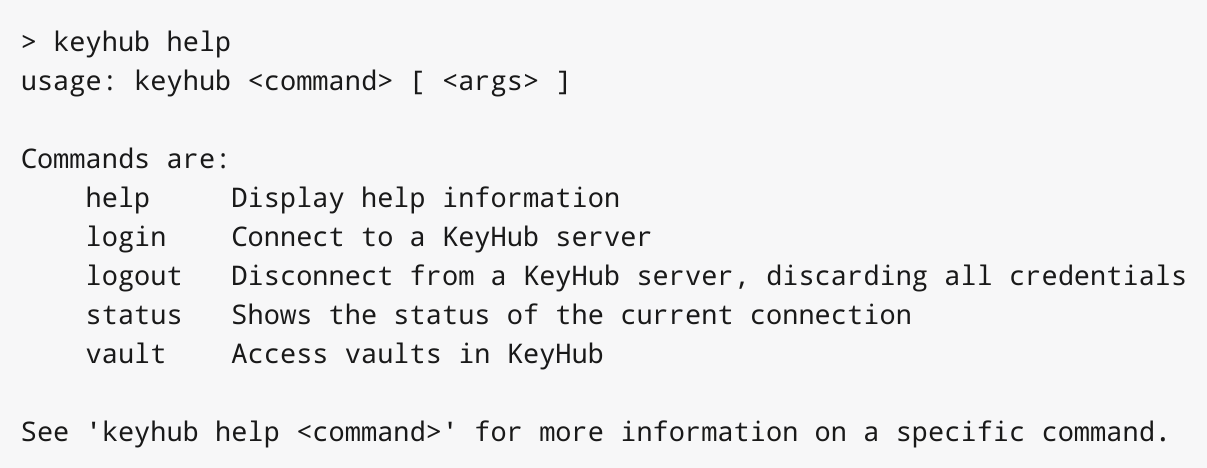
Topicus KeyHub command line interface
TKH-630 TKH-632 A brand new command line interface (CLI) is introduced in Topicus KeyHub 10. This first release of the CLI allows reading, manipulating and adding records in a vault. Enroll a new VM with a randomly generated password and store it in a vault or let a script authenticate to a server using a password stored in a vault. This is all possible with the CLI. Expect many more new features here in upcoming releases.
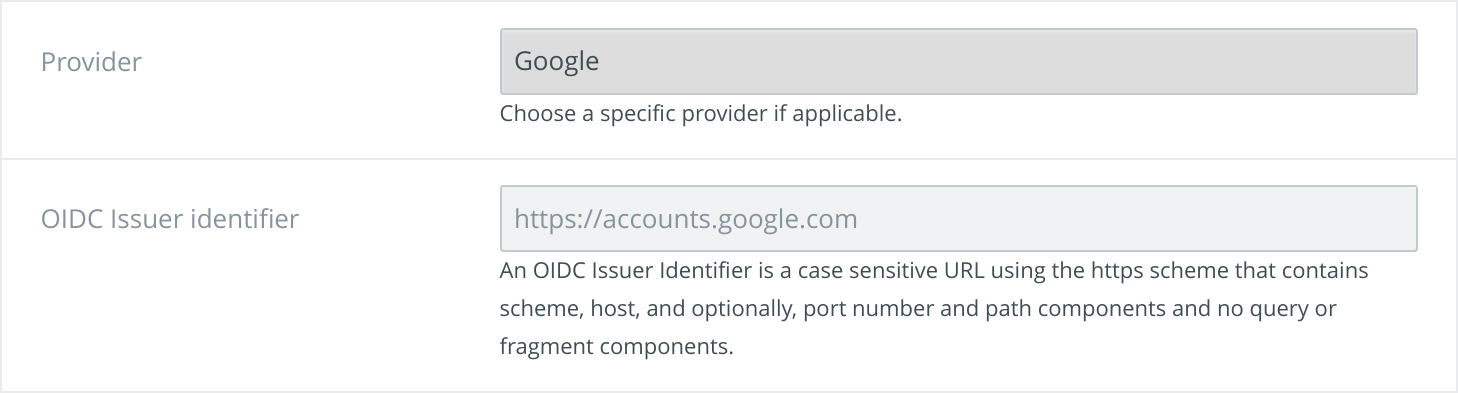
Authenticate with Google or Microsoft Azure AD
TKH-648 Special support for G Suite (formerly known as Google Apps for work) and Microsoft Azure AD was added to the OIDC directories. This not only greatly simplifies configuration but also lets you restrict accounts to a certain domain.
Small improvements
The following smaller improvements and bugfixes were made:
TKH-595The bookmarks are now correctly updated after adding or removing a vault.TKH-634Removed all references to the old project name Heimdall.TKH-638TKH-642Fixed 2 errors with registering on an OIDC directory.TKH-640Improved handling of requests on blocked resources.TKH-641The error page is now stateless, reducing the risk of DOS.TKH-643Fixed some layout issue on mobile devices.TKH-644Fixed an error with adding multiple groups with the same name to a linked system.TKH-645Unlocking the vault now checks the password before prompting for 2FA.TKH-646Fixed the checks when issuing requests which could cause requests to be incorrectly seen as duplicates.TKH-650Fixed several layout issues in the vault when using long file names.TKH-651Fixed an error with signing out on some SSO endpoints.TKH-656Always reauthenticate when changing 2FA settings.TKH-657The KeyHub console now refuses to render in an iframe.TKH-659Usernames are now hidden to other users when not needed.TKH-660Fixed handling of requests on unused SSO endpoints.TKH-661SSH public key support is now optional for LDAP systems.TKH-6652FA is now protected against brute force attacks.

